
You can’t manage what you can’t see. Even a small network generates over 250,000 logs per hours. An impossible task for a human to review. We now live in the days of sophisticated digital hackers so your concern shouldn’t be if you’re going to get hacked, but what you’re going to do when it happens.

We’ve all had a relationship go sour over time, a communication breakdown if you will. Here are 4 tips to keep communications flowing throughout the

Technology has become so richly interwoven into the fabric of our lives it would be hard to imagine doing some of our most common tasks

Introduction What would an hour of downtime cost your business? As a business owner, I’ve had many slick salespeople try to convince me of things

HIPAA Audits – The Wait is Over – It’s Real This Time As an IT professional, there are several things that always keep you up
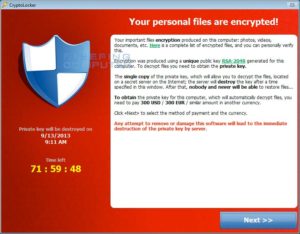
Almost every day there is a big corporation that is getting hit by one of the variance of the Crypto – Ransomware malware. For every big case that makes the news there are thousands of others that are being affected. These attacks are not going away anytime soon.
This blog is designed to further explain The Theory of Constraints and define some of the processes and applications for discovering and solving the constraints in a business setting.

In today’s environment, the core of any security strategy needs to shift from breach prevention to breach acceptance.” – Gemalto, data security firm Times they
One of the biggest challenges for any entrepreneur or business person is what Gino Wickman; author of the book Traction, calls “Letting go of the

There is not a day that goes by that you do not read in the paper or hear on television that some company has been

For two decades, the advice on phishing was reassuringly simple. Watch for bad grammar. Hover over links before clicking. Be suspicious of unexpected attachments. Your

Microsoft Copilot is sold as the productivity upgrade your business has been waiting for. Ask it a question and it pulls answers from across your

When the systems go down, most owners think about the obvious: nobody can work until they come back up. But the real cost of an
The Misconception Most Businesses Have Many organizations assume that once they move to Microsoft 365, their environment is secure by default. After all, Microsoft provides

Why AI Feels Inconsistent People are talking a lot about how smart AI is, but the reality is much simpler. AI is only as effective

The Problem Isn’t Always Obvious Most teams do not feel like they are wasting time. Work is getting done, emails are being answered, meetings are

Most Businesses Are Only Using a Fraction of It Microsoft Copilot is getting a lot of attention, but most businesses are still using it at

Customer support bots are often pitched as a way to reduce headcount or replace human interaction. In reality, the strongest return on investment comes from

Organizations collect more metrics than ever. Dashboards are full, reports are automated, and data is readily available. Yet many leaders still struggle to answer basic
Artificial intelligence tools like Microsoft Copilot are quickly becoming part of everyday business workflows. They help employees work faster, summarize information, and make sense of